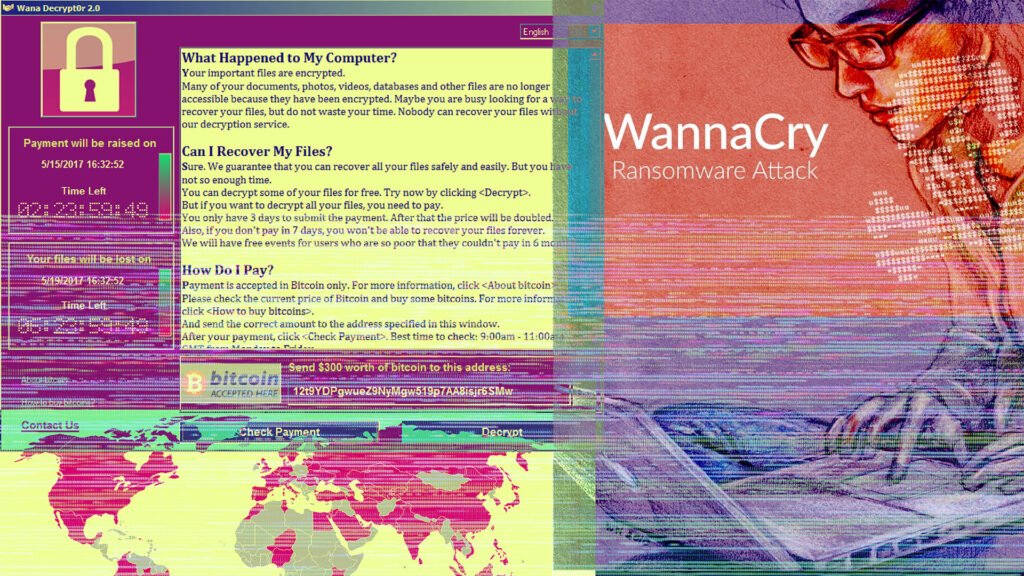
May 12 marks the fourth anniversary of the WannaCry ransomware attack, ominously named after the .wncry extension it adds to the files it encrypts. Within 24 hours of its detection, the ransomware had spread to around 150 countries, roasting thousands of computers in over 200,000 organizations.
The speed of the spread was unlike anything seen before. This piece of malware hit the National Health Service in the United Kingdom, Deutsche Bahn, FedEx, Sberbank, multiple state governments in India and universities around the world, among countless other individuals and institutions. This attack was seminal for the massive global disruption it triggered. In retrospect, the WannaCry attack offers many cybersecurity lessons to individuals, organizations and governments, and continues to show the impact of irresponsible behaviour in cyberspace.
Full extent of the attack still unknown
WannaCry was among the first large-scale disruptive attacks making the line between criminal and state-sponsored malicious activity increasingly blurry. It showed a new way of circumventing sanctions for financial gain (estimated to be between USD 150,000 and USD 386,900), demonstrating that ransomware had transitioned from a criminal gang extortion technique to a state-sponsored scheme to disrupt day-to-day activities (the NotPetya attack one month later also showed the extent of pure destruction). Although the patch for the vulnerability exploited was released two months before the attack, more than 300,000 computers were affected in the first days and more than 1 million continued to be at risk two years later.
Security researchers quickly attributed the WannaCry attack to Advanced Persistent Threat 38 (APT38), also known as the Lazarus Group from North Korea. The governments of the United States (US) and the United Kingdom (UK) followed suit by attributing the attack to the same group in December 2017. As part of its cyber diplomacy toolbox, the European Union imposed sanctions for the first time on Chosun Expo, an entity providing financial, technical or material support to APT38. The US Department of Justice has since indicted North Korean hackers for a wide-ranging scheme to commit cyberattacks and financial crimes, including WannaCry and related extortion, and attempted extortion from 2017 through 2020.
The first lesson to be learned in the aftermath of WannaCry is that identifying and charging those responsible takes a considerable amount of time, consequently exacerbating the impact of the attack on targets and victims.
An evidence-based societal perspective still missing
It is noteworthy that the ransom collected for WannaCry has not been significant from a financial point of view. The attack, however, highlighted the potency of ransomware-related disruption. Most evident was the impact on the National Health Service in the UK, where emergency rooms had to be closed and appointments of thousands of patients cancelled. We will never truly understand the extent of the damage that the attack inflicted on patients across the UK, whether it resulted in avoidable deaths or increased the suffering of patients already in the hospital system. It remains difficult to understand the full extent of the disruption because no data has been systematically collected or publicly released to date.
Four years later, we face the same challenge: there are no standards set for what data should be collected for investigation and research purposes when ransomware attacks occur. Beyond ransom demands and related financial loss, we have no indicators about the societal and long-term impact of attacks.
This is the second lesson to learn for the future: we need to work towards establishing international standards and harmonized frameworks for data collection on the long-standing impact of ransomware.
Governments and industry need to start sharing data more proactively with civil society and social scientists in order to understand the manifold ways in which ransomware impacts the lives of people beyond the immediate financial cost.
The international community failed to learn the vulnerability exploit lesson
The speed of the WannaCry spread took the cybersecurity community by surprise. As the forensic researchers took apart the malware, they discovered that it used a piece of exploit that was stolen from the National Security Agency (NSA) known as EternalBlue, which turned out to be the kingpin of the unprecedented speed of the spread. This exploit had been in possession of the NSA for years before it was stolen by hackers.
Therein lies the next lesson from this attack: the hoarding and trading of such destructive exploits must be forbidden.
While we recognize the challenges confronting the intelligence and police agencies around the world, it is imperative to introduce rules against the stockpiling of undisclosed vulnerabilities (0-Day exploits). As has been amply demonstrated by WannaCry and later NotPetya, the tradeoff between original purposes of intelligence gathering and potential risk to life and property they can cause is not worth it.
At the time of writing, it is estimated that on average 26% of the machines in various organizations are still not patched for the underlying vulnerability that WannaCry exploits. Numerous variants of WannaCry continue to be deployed every day.
This is the final lesson to take away: such destructive attacks span space and time, and don’t fizzle out in the same way that they mushroom.
WannaCry is not a story of the past. It stays with us in some mutated form, sprouting other attacks that leave society and essential services vulnerable. We’ve learned a number of lessons from this attack, but we remain insufficiently prepared for the future.
Call for data and research about the societal impact of ransomware attacks
To accurately assess the extent of harm caused by ransomware, we need to reinforce reporting obligations and make data available using international standards that capture societal impact.
The CyberPeace Institute calls for an inclusive approach to countering ransomware and continues to work on analyzing the societal impact of such attacks.
© Copyright: The concepts and information contained in this document are the property of the CyberPeace Institute, an independent non-governmental organization headquartered in Geneva, unless indicated otherwise from time to time throughout the document. This document may be reproduced, in whole or in part, provided that the CyberPeace Institute is referenced as author and copyright holder.
To contribute, please send us a message: