How cyberattacks and operations in the war in Ukraine are harming society and destabilizing cyberspace
June 3rd marks 100 days since the Russian military invasion of Ukraine which has seen intense suffering of the population further to shelling and bombing in cities across the country, as well as significant cyberattacks. Since the invasion on February 24th, the CyberPeace Institute has aggregated data on cyberattacks against two sets of targets:
1. Critical infrastructure in Ukraine and the Russian Federation essential for the survival of the civilian population and civilian objects which are all protected under international humanitarian law (IHL) and
2. Targets outside of these two countries that have been impacted by cyberattacks as a result of the war and its associated economic and geo-political context.
This data has been made publicly available and contributes to analysis of the use of cyber in war time. The tracking of cyberattacks and incidents as they become public is important in order to record these attacks and identify – where possible – the harm and risks for civilian populations. Civilians around the world can be negatively impacted by cyber attacks even if they are not directly targeted. It is therefore important to safeguard the information on cyberattacks to identify developments or clarifications of the law in relation to the use of cyber operations in armed conflicts, and for accountability including in any future judicial proceedings.
Cyberattacks and operations in the war between Ukraine and Russia
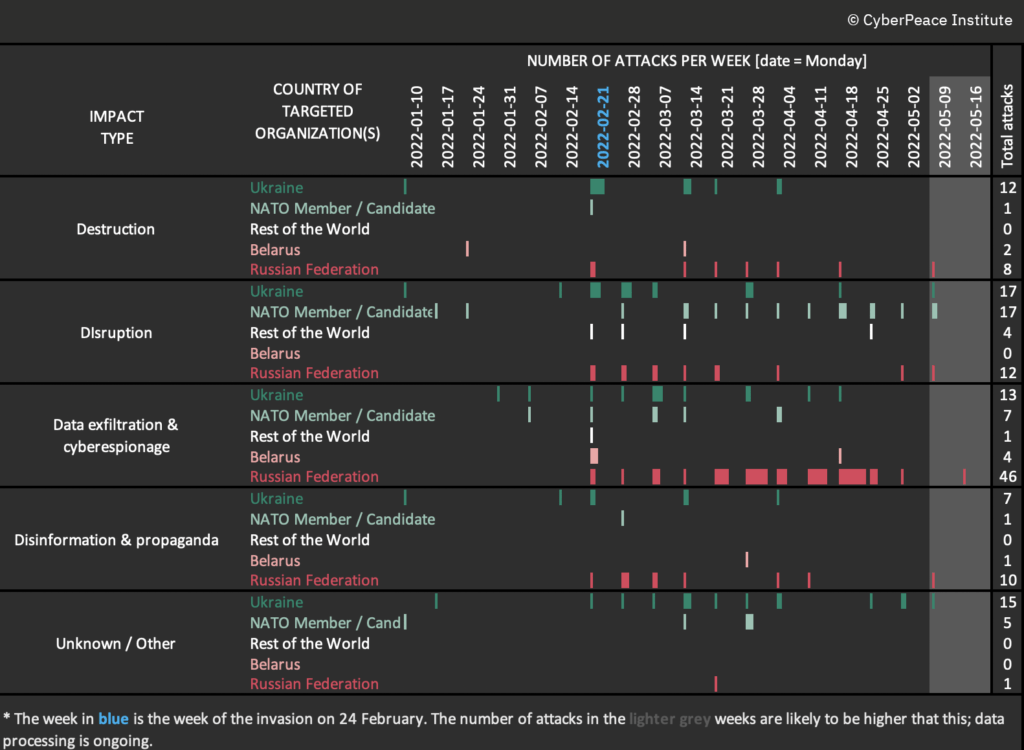
There are key takeaways from the past 100 days of cyberattacks in this conflict:
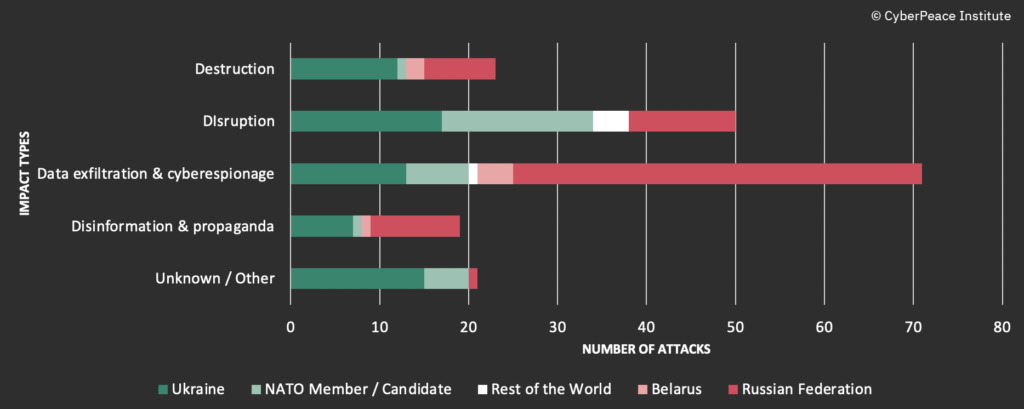
- While cyberattacks aren’t playing a major role in tactical advances of either side – cyberattacks are used as a means of destruction, disruption, and data exfiltration, in addition to the widespread use of disinformation; they have led to the destabilization of cyberspace.
- The conflict has seen a number of cyberattacks on critical infrastructure, such as communication services and electric power stations, in violation of International Humanitarian Law.
- So-called “hacktivist collectives” have played a significant role during this conflict with the primary type of attack undertaken by these actors being hack and leak-style attacks by anti-Russian actors and Denial-of-Service attacks (DDoS) on Ukrainian allies by pro-Russian actors.
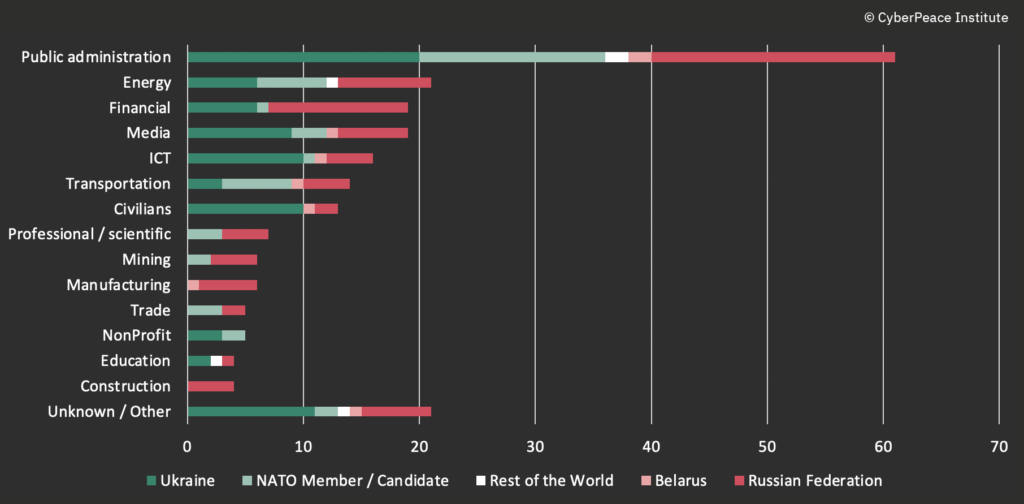
- The energy, mining and financial sectors are seeing significant numbers of attacks, both in Ukraine and Russia, as governments across the world impose and/or increase sanctions.
- Beyond traditional means of propaganda, cyberattacks are being used to spread disinformation and control the flow of information relating to the war.
Two months ago we published a blog on the harm and impact of cyberattacks in Ukraine. Since this time we have documented attacks related to the conflict and how they impact organizations and individuals beyond the borders of Ukraine.
The serious concern is not in relation to any one incident but the convergence of cyberattacks and kinetic attacks that severely impact civilians. There are many ways the civilian population can be harmed by cyberattacks. Some key observations further to an analysis of the data collected relate to 4 main types of ramifications from the cyberattacks:
(1) Destruction – attacks aimed at the permanent deletion of data or damage to systems rendering them unrecoverable. The war has seen the deployment of wiper malware targeting Ukrainian government entities and other sectors. These attacks can have long-lasting effects on organizations if they are unable to retrieve backups or reset systems.
(2) Disruption – attacks that lead to the temporary interruption of services or operations due to, for example, increased traffic or the encryption of systems. DDoS attacks have featured heavily during the conflict, both on Ukrainian organizations during the early stages of the invasion, on Russian organizations following a call to create an IT army by the Ukrainian government, and on public institutions in some NATO member countries following the imposition of sanctions on the Russian Federation. These attacks have heavily impacted the connectivity of telecommunications and internet services across Ukraine and the availability of websites in Ukraine, the Russian Federation and other parts of the world.
(3) Data exfiltration – attacks leading to the theft or exfiltration of data or the acquisition of data for espionage, surveillance or intelligence purposes. Although the latter are known practices in the context of war and geo-political conflicts, the former are attacks which have been heavily conducted by collectives of actors in the name of activism. Data, relating notably to Russian private and public organizations, is being exfiltrated and published online at a pace rarely seen before.
(4) Disinformation – attacks with a focus on the spreading of false information and propaganda, and/or the manipulation of the information space, leverage cyber and have become a feature of the armed conflict. From SMS spam campaigns spreading false information about technical malfunctions of ATMs, to cyberattacks on TV stations in which information is falsely displayed on the news ticker or deepfake videos are streamed, through to threat actors compromising email accounts in order to gain access to the social media accounts of high-profile Ukrainians in order to post disinformation.
Russian escalation – bring in the wipers
Wiper malware attack campaigns have been synonymous with the Russo-Ukrainian war. Since January, 6 significant strains of data-wiping malware – WhisperGate / WhisperKill, HermeticWiper, IsaacWiper, AcidRain, CaddyWiper, DoubleZero – have been identified targeting Ukrainian entities and organizations. Three of these were first observed to be deployed on the day before or of the invasion. The impact of these attacks has rarely been publicly reported yet it appears that they have been primarily deployed against public institutions, financial and energy companies and telecommunications providers in Ukraine. A wiper attack on a border control station on February 25th was reported to have slowed the process of allowing refugees to cross into Romania from Ukraine.
Cyberattacks and operations of a destructive nature have continued to be used as the war evolved. On April 8th, a foiled attack using wiper malware targeted electrical substations in Ukraine, if this had been successful it would have deprived roughly two million people of electricity and made it difficult to restore power. Yet, the Institute has also documented destructive attacks on Russian public institutions and financial, energy and travel management companies claimed by collectives associated with Anonymous. For example, on April 18th an attack on a Russian bank led to the exfiltration of over 1 terabyte (TB) of data including financial statements, tokens, tax forms, client information, and sensitive databases before allegedly deleting all backups to prevent data and functionality restoration.
Critical infrastructure is not spared – Communication Services impacted
The information and communication technology (ICT) sector is one of the most visible sectors to have been targeted during the war. The CyberPeace Institute has documented at least 6 cyberattacks or campaigns specifically against telecommunication service providers in Ukraine. The head of the State Service of Special Communication and Information Protection of Ukraine (SSCIP) said on May 4th that “invading forces are deliberately destroying TV and radio broadcasting infrastructure in Ukraine to take away any opportunity from Ukrainian people to get reliable information on developments in the war and the situation in Ukraine.” Although this brief was in reference to kinetic attacks, the data collected on cyberattacks against both media entities and telecommunication service providers indicate that cyber has also been used as a means to disrupt access to information.
The AcidRain wiper malware attack on Viasat’s KA satellite network in Ukraine on the day of the Russian invasion impacted a major German energy company who lost remote monitoring access to over 5,800 wind turbines. Despite the attack appearing to have been targeting Ukraine military objects, the civilian population and civilian objects both in Ukraine and beyond were impacted. Following the March 28th attack on a major Ukrainian network provider, connectivity collapsed to 13% of pre-war levels with nation-wide disruption observed and the restoration of service observed some 15 hours after the initial disruption.
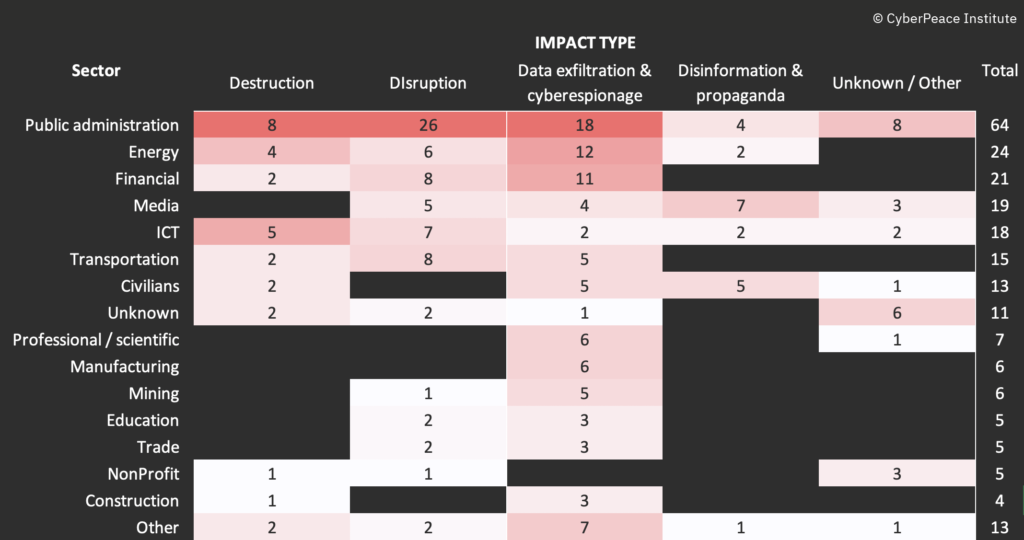
* Some attacks or campaigns have impacted multiple sectors
Civilians and collectives make waves in cyberspace
On February 26th the Minister for Digital Transformation of Ukraine, Mykhailo Fedorov, announced the creation of an army of IT specialists to fight for Ukraine in cyberspace. The consequences and potential long-term implications of this call to action – often referred to as Ukraine’s IT Army – are unknown. As the Ukrainian government declared that in the week 9-15 May, more than 240 Russian online resources were attacked by their IT Army.
Yet it is the attacks by collectives that are causing a significant stir. In their public declaration of allegiance to one party or the other, these collectives commit cyberattacks at a rate and scale rarely seen before. Since February 26th, a transparency collective known as Distributed Denial of Secrets began to publish hundreds of gigabytes of data from predominantly Russian organizations. The Anonymous collective has been particularly active in committing hack and leak operations against Russian and pro-Russian organizations since the start of the year. The CyberPeace Institute has documented 44 incidents self attributed by Anonymous of which 39 attacks in Russia, 3 in Belarus and 1 each in Germany and France but related to attacks on Russian organizations.
Collectives have played a significant role in cyberspace during this conflict with the primary type of attack undertaken by these actors being hack and leak-style attacks by anti-Russian actors but also DDoS attacks on Ukrainian allies by pro-Russian actors [see below].
Ukrainian allies and NATO countries under cyberattack
A spate of DDoS attacks in the months of April and May impacted public administration, government websites and national rail providers of governments who have demonstrated support to Ukraine. Attacks have been documented on NATO members and those who are candidates for membership: Finland, Czech Republic, Romania, Estonia, Germany, Canada, Spain, France and Italy. The collective KillNet has claimed credit for these attacks since it publicly declared war on Anonymous, a direct result of several Anonymous factions declaring they are in ‘cyberwar’ with Russia. Very little is known about the Killnet group who emerged since the invasion of Ukraine.
Many of these attacks are taking place in the geopolitical and economic contexts relating to sanctions, weapons supplies and ongoing NATO membership negotiations.
Sanctions or not? The energy, mining and finance sectors feeling the pinch
Since January 2022, the Institute has documented a number of attacks on the energy sector (notably gas) and mining (notably oil) sectors as they have seen a spate of attacks. Twelve attacks have been documented on Russian organizations primarily (8) related to the hack and subsequent leak of data whilst two attacks led to the defacement of websites / public interfaces in order to publish pro-Ukrainian messages. Six attacks have been documented against Ukrainian organizations but these are different in nature as they can be classified under the broader category of cyberespionage or wiper malware attacks.
Attacks against organizations in Germany (4), Switzerland (1), Spain (1) and the United States (1) have less tangible links to the war but are thought to have a possible link to imposition of sanctions on Russian organizations. For example, on March 2nd the Swiss-based operator of the Russian Nord Stream 2 gas pipeline said its mobile and fixed network lines were not reachable and it had shut down its website amid cyberattacks.
The financial sector in the Russian Federation has also been impacted by data exfiltration (10) and DDoS attacks (3) with twelve attacks documented since the invasion whilst Ukrainian financial organizations have been impacted by DDoS (4), wiper (1) and cyberespionage (1) attacks. Beyond the borders of the conflict, the German financial regulator BaFin has recently issued a warning to the financial sector due to the war in Ukraine following an increase in cyberattacks. As with the attacks on the energy and mining sectors, without further in depth research it is not possible to make a definitive cause and effect link between sanctions and cyberattacks on the financial sector but the Institute has certainly noted increases in cyberattacks on the sector as there has been tightened sanctions.
Controlling the information space through cyberattacks
With every war comes propaganda yet for years prior to the invasion, the Russian Federation has sought to maintain a tight grip on the information space both in its own territory and beyond. Recent years have seen a move away from propaganda – production and promulgation of political or ideological rhetoric, a one sided view to spread influence – to the use of disinformation – spread of false information as a hostile act to deliberately mislead and manipulate. Tactics ranging from the use of botfarms to reach maximum audiences through to cyberattacks to deface websites, this war’s circulation of disinformation is being waged both offline and online. Attacks on the media sector have been relentless in their attempt to influence the information space through the spread of disinformation as well as disruptions of services to limit access to timely, reliable and official information to the population in both Ukraine and/or Russia. On March 16th,Ukraine 24 television station was attacked resulting in the false reporting that the Ukrainian President had urged Ukrainians to stop fighting and give up their weapons. The program’s news ticker was hacked to display messages to appear as though they were coming from the president. On February 26th, a number of Russian domestic news websites, including TASS, Fontanka and Kommersant, were attacked and information replaced with a “tombstone” for the war dead.
Threat actors have attempted to influence information circulation through mainstream media by accessing the accounts of or impersonating high-profile Ukrainian figures, defacing websites or altering information through cyberattacks in order to spread geopolitical messages, spread disinformation and influence public opinion. Attacks of this kind are happening both in Ukraine and the Russian Federation as those with opposing geo-political views are trying to be heard.
Attacks against civilians have unsurprisingly been connected to phishing, fraud and malspam campaigns as threat actors seek to capitalize on the vulnerabilities or generosity of communities during times of crisis. Civilians were specifically targeted in an SMS spam campaign on 15th February which appears to have been timed with a DDoS attack on bank and government websites with a possible intention to spread fear and confusion.
The destabilization of cyberspace
Cyberattacks conducted in the context of this war have wide ranging consequences, not just on governments, companies and civilians but on the safe, secure and trusted use of technology.
The participation of loosely affiliated individuals in conducting cyberattacks during an armed conflict poses the following challenges and sets a dangerous precedent for any future conflicts:
- Civilians directly participating in hostilities may lose their protection as civilians accorded under International Humanitarian Law, and could be targeted by cyber or kinetic means, and/or for prosecution. This extends the potential impact of conflict to individuals and societies.
- Participation of individuals (those that aren’t employed by military or civilian elements of a government) poses a risk to individuals globally – loosely organized groups, without proper coordination, training and rules of engagement can cause collateral damage via second and third order consequences of attacks they are engaging in.
- Participation of collectives poses an attribution challenge which in turn can complicate accountability for harm caused by cyberattacks.
As we look beyond the destabilization of cyberspace resulting from a flurry of actors joining the war, the Institute has also noted other challenges for which the long-lasting impacts are yet to be uncovered. Open source technologies, often founded on the principle of collaboration, have been exploited for the spread of disinformation and propaganda, going as far as the embedding of malware. Coined as “protestware”, this new trend has raised concerns about the harm this may cause to projects and contributors.
As the world is still coming to terms with how to deal with the volumes of data leaked online from ransomware attacks, the huge volumes of data leaked online in the name of activism and protests against the war are of significant concern. The consequences of the public release of these terabytes of data containing millions of pieces of personal data is yet to be fully understood, but what is certain is that individuals are highly likely to be impacted whether or not they play a role in the conflict.
Calling for protection of victims and respect for laws and norms
The CyberPeace Institute is tracking cyberattacks that target critical infrastructure essential for the survival of the civilian population and civilian objects, and targets that have been impacted by cyberattacks as a result of the war and its associated economic and geo-political context. It is important to underscore that such attacks should not be directed against critical infrastructure and civilian objects whether in wartime or peacetime. The CyberPeace Institute calls upon all actors to spare civilians and other protected persons, civilian objects and infrastructure which are ensuring the delivery of essential services in line with international humanitarian law. This is an obligation of all parties to the armed conflict. Respecting this law is important to save lives and reduce suffering.
There will need to be continued analysis of the use of cyber, and an understanding of these attacks from the perspective of applicable laws and norms, as well as accountability for attacks which have breached international law – e.g. that were disproportionate and indiscriminate. As a contribution to this endeavor, the Institute will continue to monitor cyberattacks used in the context of the ongoing Russian-Ukrainian war including a new site launching in June which analyzes attacks by sector.
It will be important that within the framework of the United Nations Open Ended Working Group (OEWG) and other international fora, there are lessons learned from the use of cyber in this armed conflict, including the need to be able to access accurate information in wartime, the impact on peace and security, as well as upholding the UN Charter and international law and norms of responsible state behavior in cyberspace. Advancing responsible State behavior in cyberspace is essential to ensuring an open, free, stable and secure cyberspace, and will require commitment and engagement from stakeholders from all sectors, including civil society organizations which are able to offer a better understanding of the impact of cyberattacks on the victims.
This blog was researched and written by Emma Raffray (Senior Cyber Data Analyst), with the support of the Analysis Team of the CyberPeace Institute.