Cyberattacks on NGOs: Campaign exploits on-premise Microsoft Exchange Servers to send malspam with links to malicious documents in existing mail threads
Last month, the CyberPeace Institute spotted a malicious campaign in its early stages of development targeting several Non-Governmental Organizations (NGOs). This malicious campaign is still active and through this blog we seek to shed light on how it is unrolling and how to act if you think you’ve been targeted.
Working together with our partners, we have closely monitored the evolution of the campaign, conducted forensic investigations and threat intelligence analyses to decipher its origin and purpose. We alerted NGOs.
The CyberPeace Institute noticed similarities with other more recent attacks as reported by TrendMicro in November and hitting IKEA’s email systems in early December.
How it began
On the 4th of November, the CyberPeace Institute started to see unusual e-mail messages circulating, originating from real persons, and validated as genuine by the servers. The typical content of these e-mails is constructed as a reply to an existing discussion thread and is normally written in the same language. It will typically start with a short greeting and point to two URLs. The e-mail ends with content from the original thread.
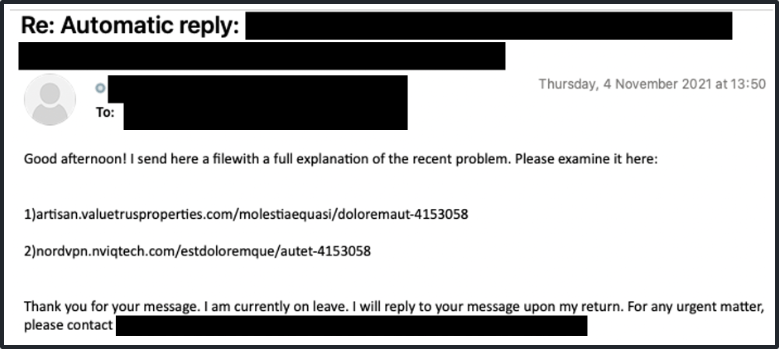
By analyzing the e-mail headers, it could be concluded that the e-mails had been sent by legitimate accounts and from the genuine servers of the entities they were supposed to come from.
The CyberPeace Institute immediately reached out to the compromised NGOs via an alternative communication channel, which confirmed that the e-mails were not legitimate, and the servers had been compromised. The Institute was able to analyze the first steps of distribution of the campaign in the hours that followed the initial detection, warn partners, and provide support to compromised entities for disaster recovery, information sharing and monitoring of the situation.
Global knowledge about the campaign among cybersecurity actors started to spread on the 8th of November and the first-stage payload was flagged as malicious by Microsoft Defender on the 9th. However, at least one victim was already hit at the very beginning of November.
The first-stage payload
Our team performed digital forensics and reverse-engineering on the attack. It was therefore possible to understand in detail how the infection occurs.
The links in the e-mail point to a zip file containing an Excel sheet (.xls). If scripts are not enabled in Excel, the user will be encouraged to enable them.
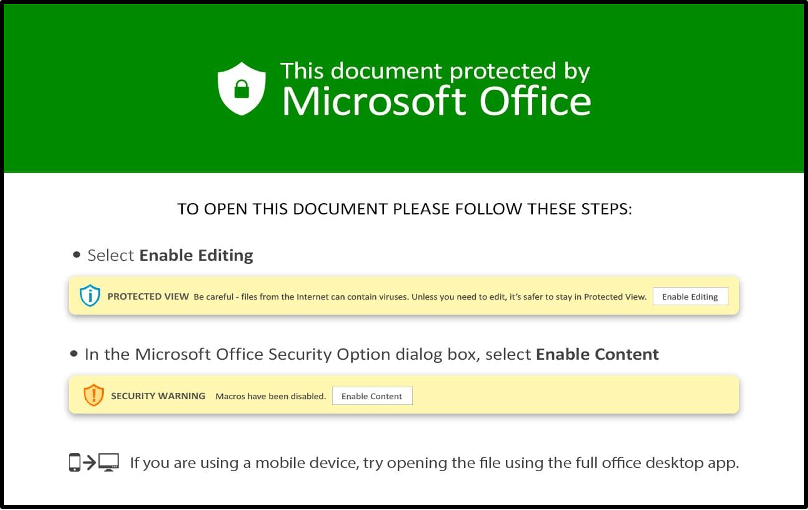
The script will then download more malicious content from third party compromised websites, drop the files in the C:\DATOP folder on the personal computer of the user who received the e-mail and modify a few registry keys to make it persistent with each opening of Microsoft Office. Consequently, the malicious content can operate only on Windows systems (registry keys are exclusive to Windows). The execution of the malicious script is transparent to the user. However, if the download fails, a pop-up may appear to warn that the script failed.
Intelligence from our partner Group-IB indicates that the first-stage payload was crafted using SilentBuilder (a.k.a. EtterSilent), a tool/service specifically designed for this purpose. Hence, crafting of malicious documents and further distribution can be delegated, which makes the identification of the attacker more difficult.
Here are some examples (disarmed) of the sources for the second-stage payload that the CyberPeace Institute discovered in the scripts. The first two match with Indicators of Compromise (IoC) reported by TrendMicro:
- https://dongarza[.]com/gJW5ma382Z/x.html
- https://headlinepost[.]net/3AkrPbRj/x.html
- https://produtoratimedeelenco[.]com.br/9E6Y322u/x.html
The second-stage payload
The malicious content, dropped in C:\DATOP on the user’s computer, will download only if some specific conditions are met and the links quickly become inoperative. It is delivered in various forms, most of the time, DLLs or executables. It has elements seemingly linking to SquirrelWaffle and Qakbot/QBot, two malware strains used in ransomware campaigns and other types of cyber extortions. They will typically become active at a later moment, when the time is right.
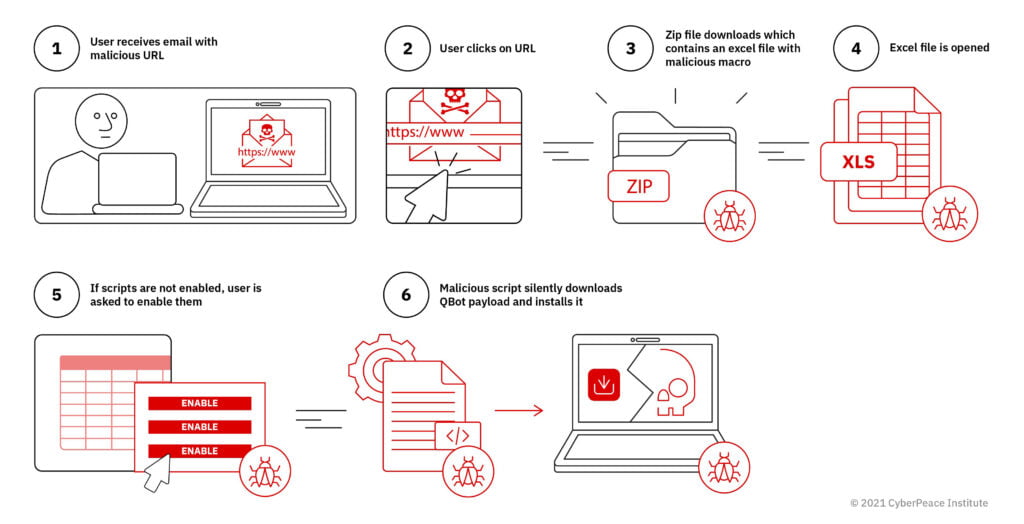
Figure 3: The QBot infection process
Based on our research to date, which classifies files as Qakbot (a banking trojan), the spreading of malicious files via malspam campaigns and findings from an ongoing investigation into the infrastructure behind the payloads, we assess this campaign to likely be of cybercrime / financially motivated nature. In some cases, it was also reported that Qakbot was used for uploading Cobalt Strike, a powerful tool for targeted attacks on infrastructures.
For more technical information and resources such as indicators of compromise and detections rules, you may consult the following publications:
- Minerva Labs: A New DatopLoader Delivers QakBot Trojan
- Truesec: ProxyShell, QBot, and Conti Ransomware Combined in a Series of Cyber Attacks
- Pan-Unit 42 GitHub: 2021-12-07-IOCs-for-Qakbot-and-Matanbuchus-activity.txt
- Talos Intelligence: SQUIRRELWAFFLE Leverages malspam to deliver Qakbot, Cobalt Strike
- Intel 471: EtterSilent: the underground’s new favorite maldoc builder
Initial compromise
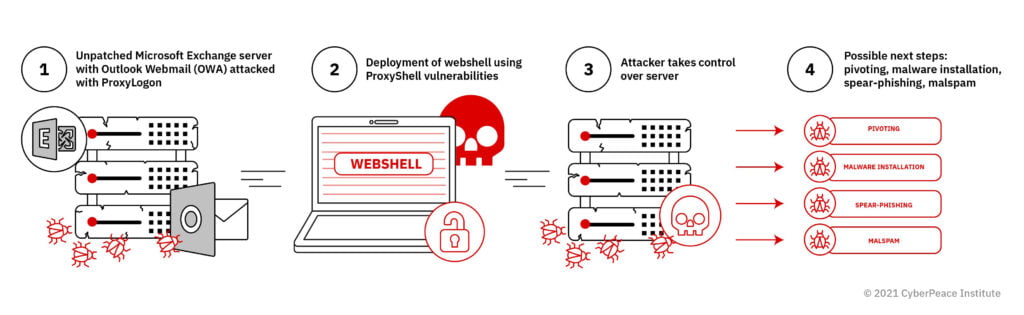
SCRT, with whom we have collaborated closely during our investigation, was able to determine that this malware campaign started with the compromise of on-premise Microsoft Exchange servers that were not up to date with security patches. More precisely, the attackers exploit the ProxyLogon (CVE-2021-26855) and ProxyShell (CVE-2021-34473, CVE-2021-34523, CVE-2021-31207) vulnerabilities to enter an Exchange server, deploy their tools and execute code remotely.
Microsoft Exchange 2013, 2016 and 2019 are all impacted. A first security update was issued by Microsoft at the beginning of March this year. A second one was released in May and some complementary vulnerabilities were fixed in July. If your systems are not up to date we strongly recommend you urgently apply the patches. If your e-mail infrastructure does not rely on Microsoft Exchange or if it is hosted directly by Microsoft (Exchange Online), this campaign shouldn’t concern you.
Potential consequences for you as an NGO
If your Exchange server has been compromised through proxyshell/proxylogon, the attacker has full control. It should be noted that such an attack is stealth and may not be detected immediately, but:
- Your partners will start to receive e-mails with malicious content, sent by you. On top of the risk of infection on your partners’ side, your image may be damaged.
- The probability is high that the contents of some or all of your mailboxes have already been exfiltrated and will be reused by the attackers to generate phishing e-mails in your name, even if your servers have been resecured after the initial compromise.
- The attackers may plant additional malware for data exfiltration, a subsequent ransomware attack or spying on your day-to-day activity inside your intranet and credential harvesting.
- The attackers may use your infrastructure as a weapon to conduct attacks on other entities.
- Depending on how fast and how well you manage the incident, your image may suffer even more (crisis communication).
- This may lead to a complete loss of control over your infrastructure and data, and inability to conduct your day-to-day activities.
For a user who opened the Excel document:
- The personal computer may be compromised with the QBot malware. The goal of the QBot malware is generally to prepare a ransomware attack, but other types of malicious activities may take place, such as credential harvesting and digital identity theft.
- If the personal computer is connected to an intranet, the malware can be leveraged to pivot and explore the local network. This may eventually lead to similar consequences as the compromise of the Exchange server (full control over the infrastructure).
Defensive and Recovery Steps
If your server has been compromised, applying the patches is not sufficient to secure the infrastructure. As a matter of fact, CIRCL.LU and SCRT recommend:
- Re-installing every compromised server from scratch (with latest patches available) and then recovering and copying the data over (while keeping the old servers isolated from the Internet, regarding both ingress and egress traffic),
- Verifying redirection rules and assigned privileges on the various mailboxes,
- Checking out the guidance from Microsoft and their tool for first mitigation actions,
- Initiating a full incident response process including the security review of the Exchange server and the Active Directory to address potential persistence
To prevent the compromise of servers and future attacks:
- Always keep your operating system and server software up to date with the latest security patches
- Enable multi-factor authentication where possible
- Make sure that logs are enabled on the various services and centralize them in a secure location (since attackers generally try to delete local logs to cover their tracks)
- Regularly review your Active Directory and keep it as clean as possible (e.g. by revoking unused accounts and disabling legacy protocols)
- Make regular security audits of your infrastructure
- Make regular backups of your systems, ideally with one set kept offline
To limit the possibility for the attacker to pivot and drop additional malicious payload on the servers:
- Deploy the free Microsoft LAPS solution to have unique and strong local admin passwords.
- Prevent the servers from reaching unauthorized hosts on the Internet.
If you have clicked on the links in the e-mail:
- Check the presence and contents of the C:\DATOP folder, this is an Indicator of Compromise
- An up-to-date antivirus software, including Microsoft Defender, is able to detect the threat and remove it
- Make sure that the latest security patches are installed
- Make sure that your e-mail software and internet browser are up to date.
Additional precautions you can take as a user:
- Do not use the administrator account for your day-to-day work; create a user account with low privileges and powershell limited by default
- Disable scripts by default in Microsoft Office.
For more information about ransomware, tactiques, techniques and procedures, and further recommendations, the following publications from Group-IB are a recommended read:
How can the CyberPeace Institute support you
If you are an NGO, we may help you on the technical aspects directly or via the CyberPeace Builders, our global network of corporate cybersecurity volunteers.
We investigate and document what happens in cyberspace to empower decision makers with the right facts so norms and regulations can better protect us all in cyberspace. You can play a role in building cyber peace: do not hesitate to contact us, whether you have been attacked or not.
The CyberPeace Institute is grateful for the support provided by Group-IB and SCRT in investigating this malicious campaign. SCRT is a Swiss company dedicated to information security and incident response. Group-IB is a global cyber intelligence company that specializes in investigating and preventing hi-tech cybercrimes.