At the CyberPeace Institute, our mission revolves around safeguarding the most vulnerable in cyberspace. Yet, have you ever considered the impact of cyber threats on organisations like ours?
Through analysis and in our daily work, we are witnessing a rise in attacks on NGOs, a trend that directly involves us, too. Instead of casting blame and fostering shame – openly sharing real experiences of cyber incidents has proven be a powerful tool for threat prevention.
As a collective, we have all encountered the disruptive force of cyber attacks. This blog serves as a candid exploration of our experiences over the past three years so we can learn together.
Phishing incidents
In most cases we face phishing incidents, which fortunately we have spotted every time.
These attacks come in various forms, from broad-scale outrages to targeted spear phishing. Spear phishing targets specific individuals or organisations containing social engineering features. This means, that they are carefully thought out and tailored to the characteristics or activities of an individual or an organisation.
One notable incident occurred in late February 2021 when preparing to publish our annual report. One of our employees received the following email seemingly from our HR department, urging them to review an attached document.
| From: Cyberpeaceinstitute <[email protected]> Date: Tuesday, 23 February 2021 at 14:29 To: NAME LASTNAME <[email protected]> Subject: Update on Cyberpeaceinstitute at 23 February, 2021 Dear xxxxxxxxx Attached is your Benefit Report from Cyberpeaceinstitute Human Resources In order to properly apply your payment to your account, please ensure that the details attached is referenced in your remittance. Kindly review and approve the compliance section so we can proceed. <attached .htm document> Cyberpeaceinstitute HR Department |
Suspicion arose due to the email’s unfamiliar sender and a syntax error regarding our Institute’s name. Our colleague promptly reported the incident to our Information Security team.
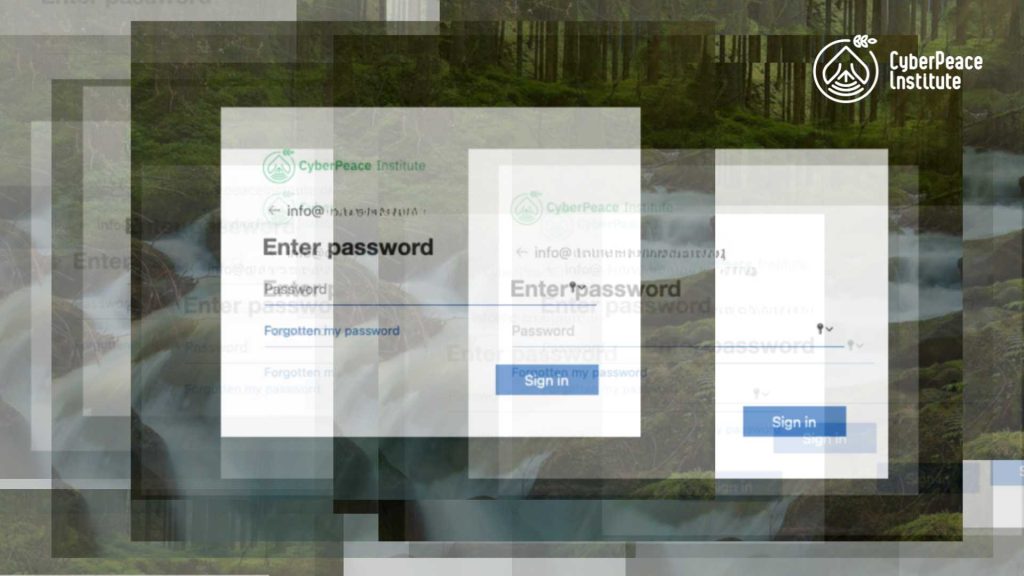
Reading the email is harmless. However, the attack is designed to lure the recipient into clicking on the attached document, which is a .htm file. An analysis of the email by our IT team revealed a sophisticated spear phishing campaign. Clicking on the attachment would redirect the user to a fake Microsoft Azure login page, indistinguishable from our official login page showing the CyberPeace Institute logo. This is a classic example of credential theft attempts through a spear phishing campaign, meaning that the incident was specifically designed for the CyberPeace Institute.
How it works: When any credentials are entered, the fake login page will claim a password or a time-out error. The credentials that have been entered are then harvested by the attacker. This login page looks legit, because it has exactly the same appearance as the Institute’s login page which has custom elements such as the background picture and the logo. Setting up a fraudulent login page is a walk in the park. Our organisation’s Microsoft Azure login page, open to the public, can be easily replicated. Simply input a valid email address of the CyberPeace Institute into the Microsoft login field, and the page instantly adopts our custom design, showcasing our logo and background picture.
Spear phishing campaigns are common and easy to set up with only a few social engineering features. Cybersecurity training and raised awareness can minimise the risk of a successful attack.
DDoS attacks
Besides phishing attacks, the CyberPeace Institute’s website has experienced two DDoS attacks, both orchestrated to target us specifically. DDoS attacks – which is short for distributed denial-of-service attacks – aim to overload a website with traffic by accessing it with more devices than the site can handle. This phenomenon results in the website not being accessible for a certain amount of time. While easy to execute, the impact of DDoS attacks is considerable – especially for vulnerable groups in conflict zones reliant on uninterrupted access to vital information.
Since the conflict in Ukraine started, our research showed that the number of DDoS attacks within Ukraine, but also other countries has increased.
When the DDoS attack targeted our Institute, it was aimed at shutting down the Cyber Attacks in Times of Conflict platform which is tracking cyber attacks within the conflict in Ukraine. The attack was supposedly a response to the positioning of Switzerland in the conflict, but certainly to the work of the CyberPeace Institute as an NGO tracing cyberattacks in the conflict.
Our cyber conflict platform was down for five minutes, which is the amount of time our defence spent mitigating the attack. Our analysis showed this was a very extensive DDoS attack with 1.34M http requests temporarily rendering our platform unavailable.
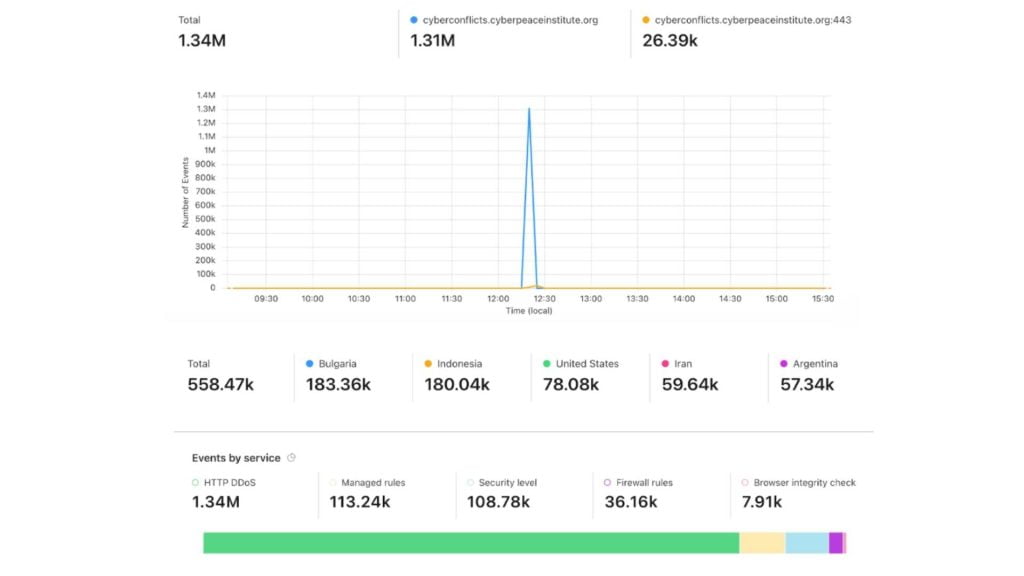
Through our investigation of the attack with the help of MALTEGO, the top five IPs were quite revealing. The modus operandi became clear to us due to the infection of the device by the ZombieBoy Malware that matches via THOR’s Yara signatures.

Third-party partner attack
Stéphane Duguin, CEO of the CyberPeace Institute explains this phenomenon as follows: “A connected ecosystem is only as strong as its weakest link. One can practise the best cyber security in the world – however, if someone working with you intensively is poorly secured, you are as well. The challenge is to ensure that everyone has the capacity to get their maturity to the same level and also share information about threats.’’
Many organisations, including ourselves, rely on cloud services in their daily work which help us organise knowledge. Any external link exposes us to potential cyber threats, as we have experienced in the recent past.
In 2022, the CyberPeace Institute encountered two incidents involving our third-party partners. In August, the password manager “LastPass” faced a security breach, but fortunately, our data remained secure. In November of the same year, another cloud tool, “Winbiz,” also suffered an incident. Although our data was unharmed, we faced a month-long disruption in accessing the tool.
The following year, 2023, brought three additional third-party partner attacks. In January, “LastPass” experienced an incident again, prompting us to switch our password manager. In July, “JumpCloud” became a target, fortunately with no impact on our services. In the same month, our partner “The Hague Hub” encountered a security breach, exposing data, possibly including personal information about a colleague of ours.
Helping other NGOs with our expertise and through our experiences
Through this retrograde on the cyberattacks that we have suffered at the CyberPeace Institute, it becomes clear that we are no different from other NGOs. We are directly targeted, because of our activities as an NGO working towards peace in cyberspace.
Similar challenges confront other NGOs, such as the creation of fake websites mimicking legitimate ones. Picture this: a misleading website created for an event, prompting individuals to sign up online and share their personal data. This type of attack unfolds on multiple fronts, with attackers harvesting personal information from individuals who believe they are interacting with the NGO’s authentic website. Beyond the immediate risk of a significant data breach, such phenomena inflict lasting damage by eroding the trust that the public places in an organisation. The consequences extend far beyond mere data compromise, underscoring the profound impact of cyber threats on organisational credibility and integrity.
What sets the CyberPeace Institute apart is our inherent commitment to cybersecurity. With experts in-house, we have been able to effectively mitigate attacks. Recognizing that many NGOs lack these specialised skills, we extend our support through our initiatives like the CyberPeace Builders or the Humanitarian Cybersecurity Center (HCC). Our mission is to assist NGOs in fortifying their cybersecurity defences, fostering resilience in the face of evolving cyber threats.