While passwordless authentication solutions are slowly gaining traction, for the time being, most services and platforms continue to require passwords to authenticate their users.
There are 300 billion passwords being used globally, on average 40 passwords per person. According to a breach analysis, 23.2million global victim accounts in 2019 used 123456 as their password.
To keep you and your accounts safe, the CyberPeace Institute’s top two recommendations are the use of a password manager (comparison found here) and multi-factor authentication. For the rest, we have summarized three simple steps to follow.
Step 1: Check the Security of your Current Passwords
Here is a list of criteria to assess the security of your current passwords:
Has your email address and its associated password been part of a previous leak?
>>> You can check this via Have I Been Pwned?, Firefox Monitor, or Google Password Checkup if you have a Google Account. While you should not enter your current password into the Pwned Passwords test, you can download a dataset of compromised passwords.
- Are you using a password across multiple accounts?
- Is your password among the most common passwords?
- Is your password weak?
>>> You can check this (using a simulated password, not your real one) via How Secure is My Password?, The Password Meter, Kaspersky’s Secure Password Check, or My1Login’s Password Test. REMEMBER TO NEVER ENTER YOUR REAL PASSWORD; you can simulate a similar password (i.e. length, number of letters and symbols, complexity).
If your password matched one or more of these criteria, then we recommend considering a password change.
Step 2: Creating a New Password
When creating a new password, you should always make sure that it is:
Unique: Avoid reusing passwords or a similar composition (cf. dog123 and cat456).
Anonymous: Avoid including any personal identifiable information in the password (e.g. name, birthday, address, pet’s name, etc.).
Complex: Complex passwords that are still easy to remember are sentences, such as Passw0rdDayIsTheB3stDayOfTheYear? Try using at least 12 characters, containing uppercase and lowercase letters, numbers, and symbols. Avoid including the platform’s name.
Strong: Pay attention to the password strength analyzers that many sites offer.
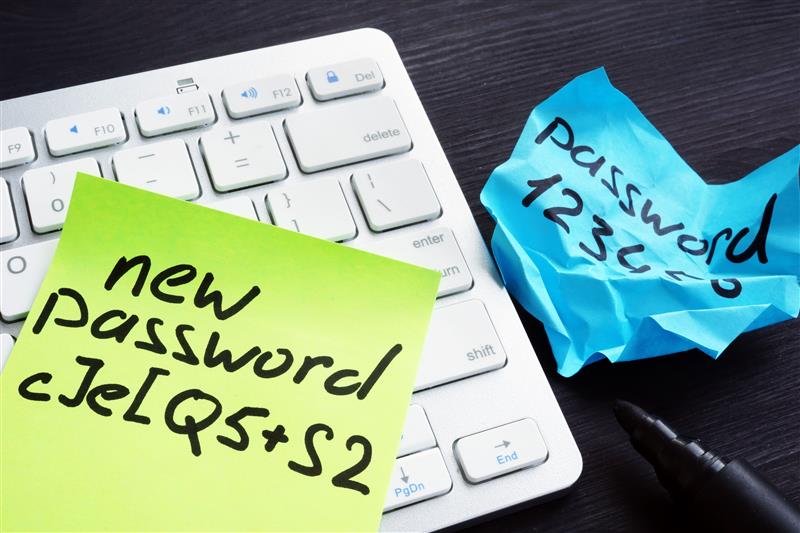
Creating a strong password is only half of the battle. You also need to keep it secure!
Step 3: Keeping your Password Secure
A password is only as strong as the human behind it. Often times, human error is the greatest vulnerability in data security. Thus, we recommend to:
- Never share your passwords via emails or instant messaging
- Never keep your passwords in text files
- Never save your passwords in browsers
- Avoid entering your passwords in other people’s devices
- Avoid sharing your passwords with friends, family, and colleagues
- Avoid entering your passwords when using public WIFI connections
- Always log out when leaving your devices unattended
- Always think twice before entering your password whenever you are contacted and asked to provide it. If an email, message, or password prompt seems “phishy,” there is a high likelihood that it is. As with other social engineering attacks, stop, investigate, contain, report!
Other useful security tips and tools can be found here.
…
The CyberPeace Institute is an independent, non-profit organization with the mission to enhance the stability of cyberspace. It does so by supporting vulnerable communities, analysing attacks collaboratively, and advancing responsible behaviour in cyberspace.
Copyright: The CyberPeace Institute