Big Statements Matter Little for Victims
In November 2019, coinciding with the onset of the COVID-19 pandemic, Maze became the first ransomware operator to, not only encrypt, but also publish the data of a victim. This marked perhaps the most drastic evolution of the ransomware modus operandi in the form of so-called double extortion. Since then the number of operators adopting such tactics has increased drastically, enabling ransomware operators and their affiliates to request much higher ransom payments. However, it has also helped to shed some light on the cybercriminal ecosystem as ransomware operators have had to maintain public-facing data leak infrastructure as well as nurture their brand reputation – a crucial component of the double extortion business model.
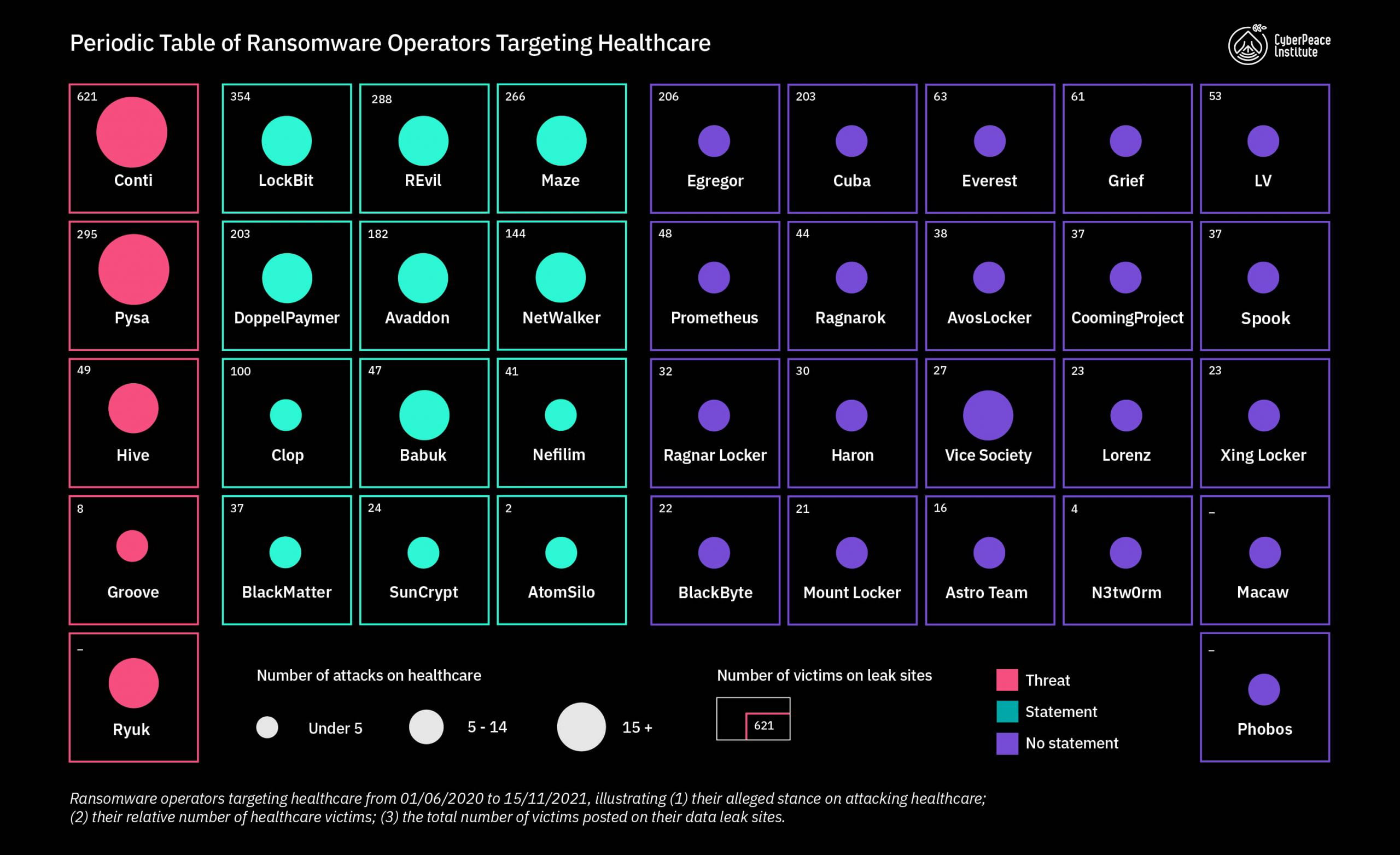
The CyberPeace Institute has tracked such ransomware attacks against the healthcare sector and those who perpetrate them as part of the Cyber Incident Tracer (CIT) #HEALTH. The platform has documented at least 39 ransomware operators that have attacked one or more healthcare organization(s) across 27 countries over the past 18 months. These attacks have not only occurred in the background of the pandemic but also in spite of many of these groups’ claims that they would not target healthcare organizations. While publicizing the statements with which these groups market themselves (and perhaps even attempt to lay false trails) remains problematic, such statements nevertheless provide an opportunity for analysis if done critically and with complementary data.
Healthcare as Collateral Damage
The CyberPeace Institute examined darknet publications, correspondence, and interviews of the most prominent ransomware operators and identified 12 groups that have made promises not to attack healthcare organizations while in fact doing exactly that. This discrepancy can partially be explained by the type of organizations they perceive as belonging to healthcare. Pharma companies were defined as legitimate targets by most as they allegedly “benefit from the current pandemic.” All 12 of the groups either singled out “hospitals” as being off limits or used vague terms like “medical organizations,” leaving room for broad interpretation. Nonetheless, at least six of these ransomware operators have also attacked hospitals.
According to three ransomware operators, such attacks can happen by mistake, in which case a decryption key would supposedly be provided “free of charge.” As noble as they may try to present this gesture, intent matters little for the victim(s). Once the ransomware is deployed, the damage is done. Perhaps the most illustrative example of this is DoppelPaymer’s attack on the University Hospital Düsseldorf on the night of September 11, 2020. The attack made global headlines as tragically a 78-year old woman passed away after she had to be diverted to a hospital 32 km away. Despite the attackers providing a decryption key shortly after being informed that they had attacked the “wrong” target, data could still not be retrieved from the hospital IT systems for the following weeks.
Healthcare as a Target of Choice
Cyberattacks against healthcare organizations are not always the result of careless targeting “mistakes.” For some, it is by design. In October 2021, a threat actor believed to be associated with Groove ransomware, specifically requested network access to hospitals in the US and EU. This seems to be more than just empty promises. While the sample size of victims on Groove’s data leak site remains relatively small, it is nonetheless indicative. With three out of eight (or 37.5%) victim organizations on the data leak site constituting patient care facilities, Groove has the highest percentage of healthcare targets vis-a-vis other sectors.
For others, this targeting is less explicit but the numbers speak volumes. According to Mandiant, 20% of targets of the prolific FIN12 threat actor constitute healthcare organizations. FIN12 has been linked to the Ryuk ransomware, which was used in the 2020 attack against the United Healthcare Services (UHS). The attack disrupted services across all of the healthcare network’s 400 locations. Authorities had previously issued alerts for the healthcare sector, explicitly warning about Ryuk. Similar alerts have also been issued for Conti, Hive, and Pysa. Their respective percentage of healthcare targeting constitutes 4%, 12%, and 9%.
Healthcare as a Target of Indifference?
There is a third category of ransomware operators, namely those that have remained silent on the matter. The majority of the ransomware operators referenced on the CIT platform fall into this category. For 15 of 21 of these groups, it correlates with their lower online presence (e.g. less elaborate data leak sites and communications) and lower victim count. However, the remaining six exhibit similar targeting tendencies as the likes of Hive, with an average healthcare targeting of 12%. At best, this is the result of indiscriminate spray and pray tactics, such as phishing campaigns or Remote Desktop Protocol (RDP) brute force attacks. At worst, it is an indicator of malicious intent by the ransomware operators and/or their affiliates towards a crucial sector in a period of crisis.
Attacks on healthcare organizations by ransomware operators in the past 18 months. ( The visual was created with the help of Kineviz and their GraphXR analytics platform.)
Conclusion
Regardless of whether the targeting of healthcare organizations is by mistake, design, or indifference, ransomware operators are acting with impunity and are de facto defining what organizations constitute legitimate targets and what is off limits. However, their simplistic distinctions ignore the complexities and interconnectedness of the healthcare sector, in which attacking pharmaceuticals during a pandemic can have an equally devastating human impact as attacking hospitals. The underlying issue here is and remains the lack of accountability, which has enabled these groups to act with near impunity and from a position of power. This is partially due to the fact that the analysis of such actors has often relied on the information that these groups themselves are willing to show under the guise of their brands. However, these brands are only a vehicle and ransomware merely a tool. Thus, to hold their culprits accountable requires looking beyond just their ransomware brands into the cyber (criminal) ecosystem.
A follow-up blog post will attempt to shift the analysis away from just the ransomware operators to their respective place in the past, present, and future of the cyber (criminal) ecosystem.
This blog is part of the new Series: Reconceptualizing Ransomware researched and written by Bernhard Schneider (Cyber Data Analyst), with the support of the Analysis Team of CyberPeace Institute.
© Copyright: The concepts and information contained in this document are the property of the CyberPeace Institute, an independent non-governmental organization headquartered in Geneva, unless indicated otherwise from time to time throughout the document. This document may be reproduced, in whole or in part, provided that the CyberPeace Institute is referenced as author and copyright holder.
Compared to other threat actors, ransomware operators have kept a much greater public profile via their leak sites (or so-called blogs), interviews, or social media presence. This is partially due to the role that brand reputation plays in the success of double extortion.
To increase the chance of ransom payments, ransomware operators have to ensure their victims that they are predictable negotiation partners. Victims that pay a ransom have to know that the ransomware operator will provide a decryption key, delete stolen files, and not re-victimize them. Likewise, by publishing the data of prior victims on their leak sites, ransomware operators further demonstrate the consequences of “non-compliance.”
As ransomware operators increasingly rely on affiliates for initial network access, they have come into direct competition for these actors. As a result, ransomware operators have often marketed themselves as profitable business partners. In this light, leak sites do not only serve the purpose to punish victims but also to advertise high-profile targets to potential affiliates. As a further marketing strategy, ransomware operators have presented the technical capabilities of their ransomware on dedicated “partner” or “client” pages.
“We don’t play with people’s lives.”
SunCrypt
"ready to [...] fu** hospitals in Italy"
Groove associate
“Nothing personal it’s strictly business.”
Lorenz