ANONYM
A private knowledge discovery platform for non-governmental organizations
Our Partners

Partisia Blockchain technology

Tuneinsight Partner
Post quantum homomorphic encryption IOC match platform
Post quantum homomorphic encryption IOC match platform
Homomorphic Encryption
Automation
Web interface
Elasticsearch logging
The pilot applies this technology to perform cross-matching of indicators of compromise across five already-identified NGOs. The solution is based on Private-Set-Intersection primitives.
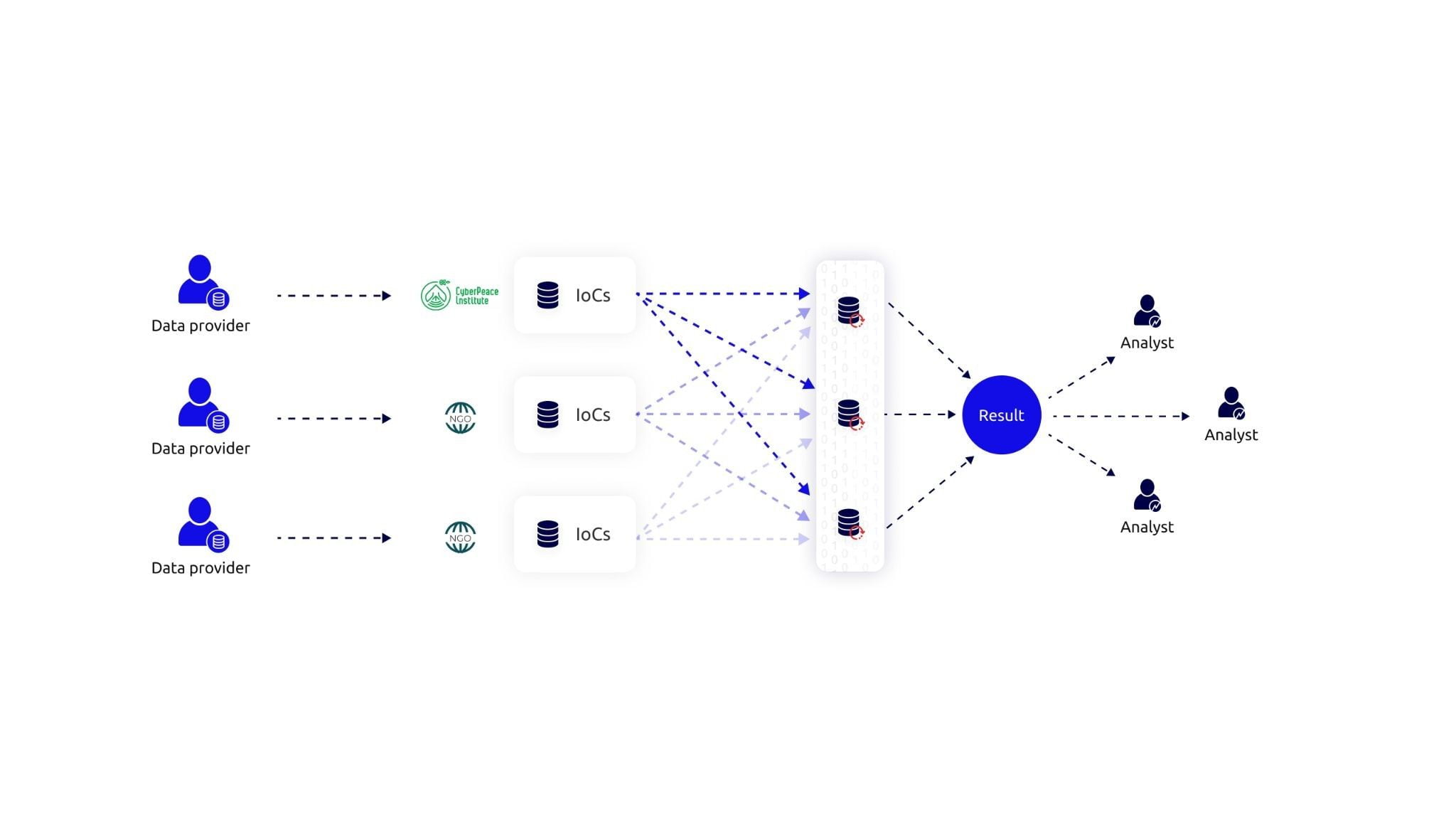
The pilot applies Tune Insight’s technology to perform cross-matching of indicators of compromise across five already-identified NGOs. The solution is based on Private-Set-Intersection primitives available in Tune Insight’s toolset.
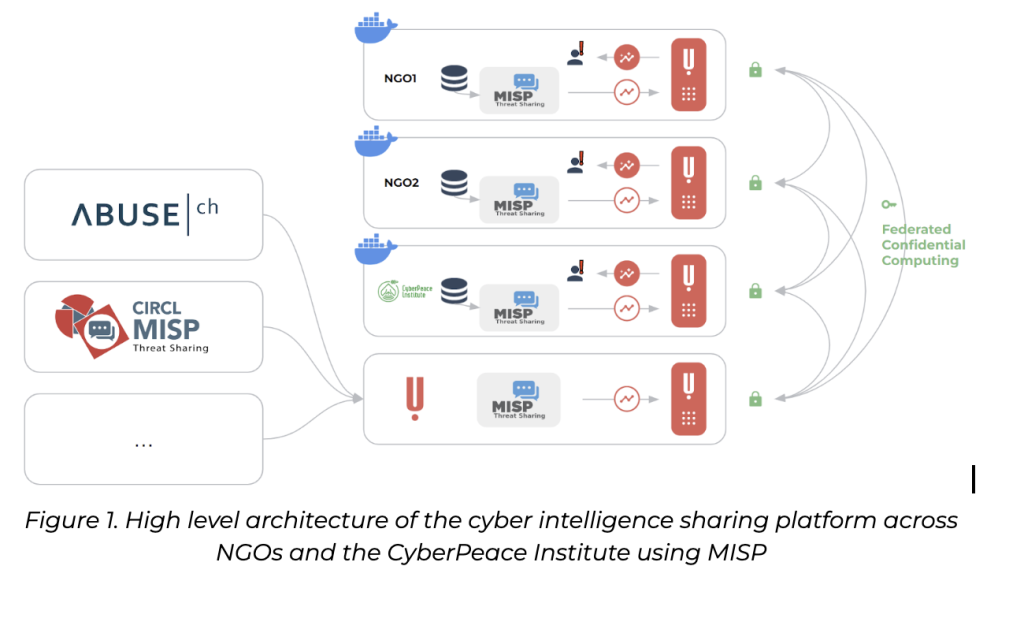
Each NGO and CPI will locally deploy a node of Tune Insight platform each, and connect it to the local data storage of IoCs (either a local MISP or a set of CSV files). The platform can manually or automatically launch matching and aggregation routines (e.g., whenever there is new information loaded at one of the sites or periodically), allowing for three levels of confidentiality for the IoCs (Hidden, CPI-only, or Open).
This enables different possible outcomes
The result of the computation for each NGO is the indication of which of their IoCs found a match in the network, without disclosure of which other NGO matched. NGOs can then take action on the found matches, including the possibility of resorting to CPI to act as broker.
CPI and the matching NGOs will get the result of the matched IoCs; CPI will be able to follow-up with the matching NGOs, as the trusted broker, to dive deeper into the found matches.
CPI triggers an automatic or manual IoC analysis that returns the percentage of all connected NGOs affected by each given IoC. For IoCs deemed non-confidential, the NGOs will have the option of clear sharing with CPI, enabling further analytics on these data.
Solve the problem of trust and discoverability by using the Partisia Blockchain as a backend Zero-Knowledge technology
Blockchain
Open Source
No Installation
Web Interface
- The scaling challenge: How can we allow NGO’s that will not rely on trusting a majority of node operators, while still not compromising the efficiency of the solution.
- The Multi party computations done in the MVP is created with an honest majority security model. This means that the NGO’s participating must trust that the majority the 4 organisations running the nodes, do not collude and share data between them. If half of the nodes were to collude by sharing data between them, it would be possible for them to “unlock” the secret shared data, thereby exposing what NGO’s has share the IoC’s.
- The honest majority model is chosen since it is secure and faster to execute. While a dishonest majority is very secure but not efficient to execute.
Our solution: a hybrid between a honest and dishonest majority.
Free Cybersecurity for Nonprofits
Protect your nonprofit organisation against cyber threats
