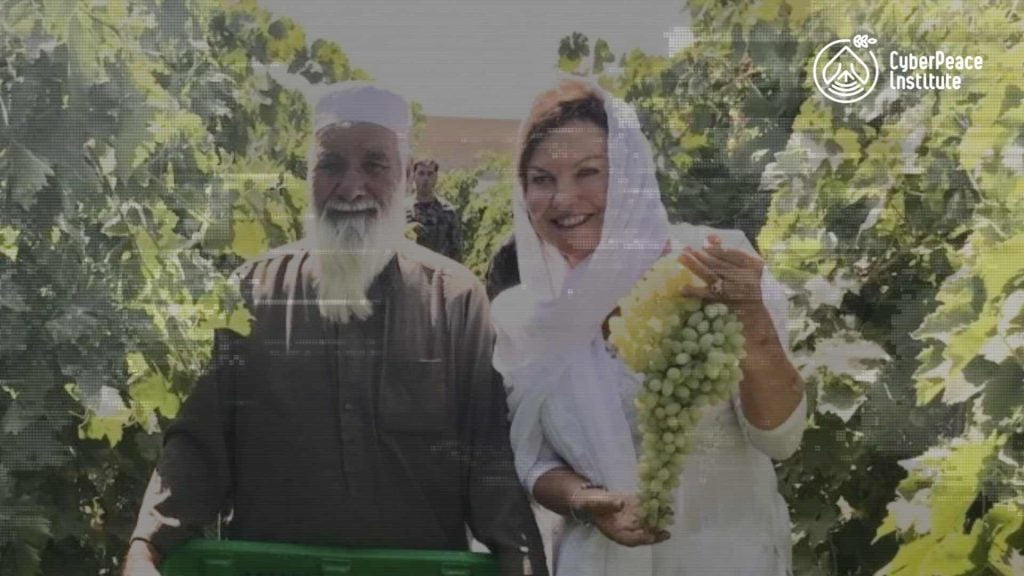
The Roots of Peace story, as told through the voice of the founder, Heidi Kühn
Organizations working to defend fundamental human rights and freedoms are among the most vulnerable to cyberattacks. The attacks not only impact the targeted entity, but the vulnerable communities that they serve. When these organizations suffer financial loss or a data breach as a result of a cyberattack, the organization must divert resources to address the attack – meaning that they may be unable to provide critical services and protection to the regular citizens affected by violence or armed conflicts, or whose livelihoods depend on these organizations. Even more, these organizations may hold highly sensitive data related to the communities they serve; a breach of this data may itself put lives directly at risk.
“I didn’t even know that it was possible,” admitted Heidi Kühn, CEO and Founder of Roots of Peace, a humanitarian non-profit organization with its vision of transforming Mines to Vines – replacing the scourge of landmines with sustainable agricultural farmland.
It was mid-January 2020. Returning from a business trip to Vietnam and China, Heidi and her husband Gary were met by the Finance Director of Roots of Peace who asked about the recent US$500,000 wire transfer to China. The Kühns had never requested nor approved such a transfer.
“That was the gut-wrenching moment when we realized that our footsteps had been monitored, our emails with a trusted bank had been violated, and we were the victims of a series of sophisticated cyberattacks,” Heidi Kühn said.
What happened to Roots of Peace?
While travelling to China, the attackers orchestrated communication between the headquarters of Roots of Peace in California which requested a prompt US$500,000 wire transfer; the Kühns who «approved» it; and their local bank who transferred money from the Roots of Peace’s account to the Bank of China in Hong Kong.
As Heidi Kühn explained: “Nothing stuck out as suspicious; the request, as it seemed, came from our trusted employees working in finance. They knew personal details, for example, like wishing us a good trip to China and asked my husband to send greetings to me. The request to transfer funds to the bank in China seemed very logical, because we work in Afghanistan which shares eight miles of border with China, so we assumed that they needed supplies.”
It was a tremendous shock to learn that Roots of Peace had been hacked. “We took immediate footsteps. I literally knocked at the door of the Council General of China in San Francisco, who guided us and helped us to file a police report with Hong Kong, where the recipient bank was located. I immediately called the FBI and two agents came to our office. With full transparency we outlined the situation, and informed our technical team in both California and Afghanistan,” Heidi Kühn described the timeline of emergency actions she and her husband had taken.
“We were optimistic in the first few days that we had addressed the problem and would get our money back,” Heidi Kühn continued. “It didn’t happen. As we subsequently learned, this had been a very sophisticated attack, the money had already been moved out of the Bank of China – it was gone.”
Increasing attacks against humanitarian organizations
Roots of Peace is a resilient organization, running a successful non-profit business for 23 years, working in war-zones in Afghanistan and surviving the Taliban attack in 2014, but the sophistication of this cyberattack was something an NGO like Roots of Peace was not adequately prepared to defend itself against.
“After the attack, I felt ashamed of what had happened, and that as the CEO, I didn’t prevent it. It felt like it was somehow our fault. But it was not. We have been a pristine organization and it has taken a lot of courage for us to talk about this tragedy so that others can learn from it,” Kühn said.
Through the series of attacks, Roots of Peace lost US$1.34 million. “This was devastating for a non-profit like us. We were faced with the dismal choice of either closing our business or taking a personal loan from our bank to cover the loss. We chose to take a quantum leap of faith and risk a personal bank loan tied to their family assets, rather than turning their backs on the Afghan farmers and traders who were depending on them during a critical harvest time,” concluded Heidi Khün.
It was also clear that the organization had to recover quickly; resources were required to patch systems and secure internet access for its field offices and over 200 employees, and also to continue its support and protection to thousands of farmers whose livelihoods depend on the NGO.
About CEO Fraud
CEO Fraud is a cyberattack scheme in which cybercriminals fake company email accounts and impersonate executives or trusted employees with the goal of fooling an employee, usually in finance or with financial transaction authority, into executing unauthorized wire transfers. Also known as Business Email Compromise/Email Account Compromise (BEC/EAC) this scam has resulted in a loss of USD 26 billion between 2016 and 2019 according to the FBI.
The main attack vector is a technique that combines both direct phone call and so-called spear phishing, an advanced method of creating non-legitimate emails aimed at well-chosen targets within an organization. Cybercriminals disguise themselves as trustworthy individuals and create stories which victims believe. The victim is put under pressure via a flood of calls and/or emails requesting an urgent wire transfer (for example, a deal that must be closed as fast as possible, a last minute supplier bank account change, a secret merger abroad, urgent equipment purchase for a critical project, etc.). The malicious actors typically prepare the attack by getting to know the victim from social networks and gaining access to sensitive information via email-spoofing or by infiltrating other online messaging systems. Preparation can take weeks or months before the actual attack is performed.
But how can they create these realistic stories? Cybercriminals rely on a method called social engineering. In cybersecurity, social engineering means the use of psychological manipulation to trick people into divulging confidential information data or providing access to funds. Cybercriminals may include mining information from social media sites or other websites, direct calls, even sometimes meeting in person either the (potential?) victim or relatives of the (potential) victim. LinkedIn, Facebook and other sites provide a wealth of information about people and where they work, including contact information, connections, friends, ongoing business deals and more. An easy way to get everything needed to trick someone.
What happens next?
Exactly what happened to Roots of Peace – cybercriminals are able to convince their targets to make fraudulent wire transfers. As a company you can reinforce your own security against this type of fraud. You can:
- Train your employees on this type of fraud scheme, how to detect it and how to react.
- Train your employees on cyber hygiene best practices including phishing detection, password best practices and safe browsing.
- Set-up a two factor authentication system to secure access to your company’s email accounts and bank accounts.
- Always check before wiring transfers abroad or to countries where your company does not usually wire funds.
- Ensure strong validation for payments and fund transfers with at least 2 parties. For instance, within your company seek in-person approval for transfers of large amounts in addition to the person responsible for payment. Alternatively, arrange for your bank to block payments unless validated by a call to specific persons in your organization.
- Enrol in awareness programs which have been established in some countries by law enforcement agencies/organizations to inform companies in a certain sector when hit by a specific crimewave.
In the event that you discover you have been the victim of a fraudulent incident, immediately contact your financial institution to request a recall of funds, and notify your local law enforcement organization. Even if funds are usually difficult to regain, acting fast increases your chances of recovering part or all of what was taken.
The CyberPeace Institute is an independent, non-profit organization with the mission to enhance the stability of cyberspace. It does so by supporting vulnerable communities, analysing attacks collaboratively, and advancing responsible behaviour in cyberspace.
© Copyright: The CyberPeace Institute